Data sovereignty tips for businesses selling into EU governments - Pt 2: Long term service contracts
- Ian Makgill
- Business , Software , Technology
- 27 Apr, 2026
- 09 Mins read
If you sell long-term services into European public sector buyers, the ground is moving under your feet. In April 2026, the European Commission awarded its first sovereign cloud tender, worth €180 million, to four European providers. France is moving its civil servants off Microsoft Teams and Zoom. Denmark's Ministry of Digital Affairs has switched to LibreOffice. The German state of Schleswig-Holstein has replaced Microsoft Exchange with open-source alternatives. The Commission has published an eight-objective Cloud Sovereignty Framework that member states are starting to reuse in their own tenders. Public buyers want assurance that the data their suppliers hold cannot be reached by a foreign government, regardless of where the server physically sits.
For a non-tech firm, a construction company, an engineering consultancy, a facilities management provider, a logistics operator, an architectural practice, an accountancy, this is awkward in a particular way. You are not a software company. You did not sign up to manage a sovereign technology stack. You are running on Microsoft 365 or Google Workspace company-wide, with a handful of industry-specific tools layered on top. Now your government clients are asking questions about jurisdictional reach, subprocessor chains, and exit rights that you have never had to answer before.
The good news
You do not have to fix everything. You probably do not have to fix most things. No accountancy is going to migrate Sage to Pennylane because of one government contract, and no buyer expects them to. What you need is a defensive plan that protects government-relevant data inside the systems you already run, plus a small set of new sovereign tools for the work that genuinely benefits from them.
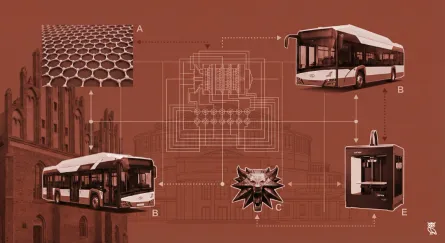
The frame for this is concentric rings. Ring one is the data that touches your government contracts directly: the project files, the email correspondence, the meeting recordings. This ring you fix properly with new tools. Ring two is the company-wide systems where some government data inevitably ends up: HR, finance, CRM. This ring you defend rather than replace. Ring three is your industry-specific tools, which you address slowly as renewals allow. Each ring is described below with concrete moves that pay off in tender responses without requiring a company rebuild.
Ring one: the contract-touching tools
For most non-tech firms, government contract data is more contained than you think. A shared drive folder per contract. An email distribution list. A handful of mailboxes belonging to the account manager, project lead, and commercial lead. A few specialist tools for the work itself. That is the ring you fix properly.
Move the contract-specific shared drives off Microsoft 365 or Google Drive and onto Nextcloud hosted on EU infrastructure. Hosting partners worth shortlisting include Hetzner, OVHcloud, Infomaniak, and IONOS. You do not need to move every shared drive in the company, just the ones holding government contract material. You can do this contract by contract as they renew.
Set up sovereign email addresses for the contract-critical roles. The account manager, project lead, and commercial lead get EU-hosted mailboxes for all government correspondence. Infomaniak kSuite, Mailbox.org, Proton for Business, and Mailfence are all credible options. Their normal company email continues for internal work. The relevant people simply have two addresses for two clearly delineated purposes.
Route government-facing collaboration through a sovereign tool. Element federates with other Matrix servers, so a single Element deployment can handle your government client channels even while the rest of the company stays on Teams. Mattermost is the close alternative, with EU-hosted options.
For project calls with government buyers, swap Teams or Zoom out for Jitsi or Whereby. Both have credible EU data stories and neither requires the buyer to install anything. This simple change, costing very little, is the best way to prevent data about meetings ending up on US servers. It also provides a visible demonstration of your commitments to the client.
Document the ring explicitly. "For contracts X, Y, Z with EU government buyers, the following tooling is used: Nextcloud hosted by Hetzner in Germany, email by Infomaniak, chat by Element self-hosted at Scaleway, video conferencing by Jitsi." That paragraph answers most sovereignty questions a procurement team can throw at you.
Ring two: the company-wide systems
Finance, HR, CRM. Salesforce, HubSpot, Xero, QuickBooks, Sage, BambooHR. These systems serve the whole business and you cannot reasonably migrate them for one government contract, or even ten. The buyer knows this. What the buyer wants to know is what protections you have in place for the government data that does end up in these systems, and how you stop unnecessary data from getting there in the first place.
The defensive moves are cheap and worth doing.
Limit what gets entered. Government contract data in your CRM should be the minimum needed to manage the relationship: contact names, contract dates, basic commercial terms. Detailed deliverables, technical specifications, sensitive correspondence stay out of the CRM and live in the ring one tooling instead. Write this down as a policy and tell anyone who handles the account.
Use the EU regions and sovereignty options your existing vendors already offer. Microsoft 365 has the EU Data Boundary configuration. Salesforce has Hyperforce EU. HubSpot has EU hosting. Sage has Sage UK and Sage France data residency. None of these solve the CLOUD Act problem in full, but each is a documented, vendor-supported step that strengthens your position. Most are configuration changes rather than re-implementations.
Add customer-managed encryption keys where the platform supports it. Microsoft 365, Salesforce, and several others let you hold the keys yourself, in an EU region. Where this is available, turn it on. It is a meaningful technical control that buyers understand.
Map what data goes where, and write it down. For each company-wide system, list what kinds of data it holds, where it is hosted, what subprocessors are involved, and what the legal jurisdiction is. This document is small, takes a day or two to produce, and answers half the questions a sovereignty-conscious buyer will ask.
For one specific case worth flagging: open book reporting. Many government contracts require detailed cost and progress data flowing back to the buyer regularly. If you are running open book through a US-hosted ERP or project accounting system, the data flow is the issue, not the storage. Two practical responses: run a parallel reporting cut from a sovereign tool (a Nextcloud workspace with structured spreadsheets, or a small EU-hosted reporting database) so the buyer-facing reports never touch the US system; or, where the data must come from the central system, document the flow honestly and add encryption-in-transit and customer-managed keys at minimum. Buyers respect specificity here. Pretending the central ERP does not exist does not pass scrutiny.
None of these moves require you to leave the platforms you are on. They require you to configure them more carefully, document them clearly, and be honest about where the limits are.
Ring three: the industry-specific tools
This is where it gets sector-specific and slow. A construction firm runs on Autodesk. A law firm on iManage or NetDocuments. An accountancy on CCH or Iris. A facilities firm on Planon or IBM Tririga. Each tool has a different sovereignty story.
The pattern is the same as ring two. Use the EU options the vendor offers, turn on customer-managed keys where possible, write down what data sits where. For the tools with the worst sovereignty story, ask the vendor what their roadmap looks like, and put the answer in your evidence pack so a buyer can see you have asked. Nemetschek (parent of Allplan, Graphisoft, and several other CAD and BIM tools) is the European counterweight to Autodesk worth knowing about. iManage has EU-hosted options. Some accounting platforms are genuinely European already.
If a tender for a specific high-value contract demands more than configuration can deliver, that is the moment to investigate a substitution. Otherwise, defend the systems you have, document them well, and treat any vendor who refuses to engage on sovereignty as a renewal candidate.
Ring four: identity and endpoints
You will not migrate off Microsoft 365 and Active Directory casually, and you should not pretend to. What you can do is make the existing estate more defensible.
EU Data Boundary plus customer-managed keys, mentioned above, applies here too. Beyond that, consider adding a European identity layer for government-contract users specifically. Signicat (Norwegian) and IDnow (German) handle identity verification well. Keycloak self-hosted is the open-source option for full sovereign identity management.
For endpoints, dedicated project laptops for the highest-sensitivity government accounts give you a clean story without solving the whole-company problem. A small estate of EU-configured devices, used only for government work, is straightforward to set up and easy to explain to a buyer.
What this looks like across three years
In year one, map the data, set up ring one tooling for active government contracts, configure EU Data Boundary and customer-managed keys on Microsoft 365, write the data flow document, and add a sovereignty section to your standard bid response.
In year two, extend ring one to new contracts as they win, configure the EU regions and customer-managed keys on the other major company-wide platforms, and start the conversation with industry-specific vendors about their sovereignty roadmaps.
In year three, address the identity layer, consider dedicated sovereign environments for top-tier government accounts, and use renewal cycles to start substituting tools where the vendor will not improve.
The bid story at any point should be specific, staged, and honest. "Government contract data and communications run on EU-hosted Nextcloud, Infomaniak email, and Element. Our company-wide Microsoft estate operates under EU Data Boundary with customer-managed keys. Our finance and CRM platforms are configured for EU residency, and we limit what government data is entered into them by policy." That reads well to evaluators because it is concrete and they can verify it.
What not to do
Do not chase ISO 27001 unless a contract demands it. A year of work, real money, and at non-tech-firm scale the honest data flow document and security policy beat it for most evaluations.
Do not promise sovereignty you cannot deliver. Promising "EU-only processing" and then having a buyer discover that your industry software ships logs to a US analytics service ends reference relationships. Honest, staged, and documented beats aspirational and vague every time.
Do not migrate company-wide systems for one contract. The ROI is not there, the buyer is not asking for it, and the disruption costs you more than the contract is worth.
The realistic bottom line
For a non-tech firm with long-term government contracts, sovereignty is a defensive posture, not a rebuild. Fix the contract-touching tools properly. Configure and document the company-wide systems as carefully as the vendors allow. Address the industry-specific tools at renewal. Be honest about limits. Most of this can be done in modest steps over two to three years, at small absolute cost. The firms that win the next cycle of EU government work are not the ones with everything already perfect. They are the ones who can show specifically what they have done, what they will do next, and when.
Frequently asked questions
Do I need to leave Microsoft 365 or Salesforce to sell to EU governments?
For most contracts today, no. What you need is to configure these platforms for EU data residency, add customer-managed encryption keys where supported, document what data sits where, and limit what government contract material gets entered into them in the first place. A buyer who will reject that on principle is rare today, though the picture may shift as the Cloud and AI Development Act lands.
What is the EU Cloud Sovereignty Framework?
It is the eight-objective evaluation framework the European Commission used to award its first sovereign cloud tender in April 2026. The objectives cover strategic, legal, operational, and environmental considerations, supply chain transparency, technological openness, security, and compliance with EU laws. The Commission has stated it intends the framework to be reused by member states, which means the eight objectives will appear, in similar form, in tenders across European public sector buyers over the coming year or two.
Can open book reporting work without sending data to US servers?
Often yes, for the buyer-facing layer. Run a parallel reporting cut from a sovereign tool, a Nextcloud workspace with structured spreadsheets, or a small EU-hosted reporting database, so the reports the buyer sees never touch the US system. Where the source data must come from a central US-hosted system, document the flow honestly, encrypt in transit, and use customer-managed keys at minimum. Buyers respect specificity. Vague promises that the central system "is fine" do not.
How much does this cost for a non-tech firm?
Most of it is cheap in absolute terms. The new sovereign tooling for ring one runs at 500 to 1500 euros a month per active government project, depending on team size. The ring two changes (EU residency configuration, customer-managed keys, data flow documentation, internal policy) are mostly internal effort rather than new software licences, and the effort is measured in days, not months. The total cash cost for a small firm is usually a few hundred euros a month plus a week or two of one technical person's time. For a large firm, the cash cost is barely visible against existing IT spend, and the work is mostly absorbed into normal operations.
Is Microsoft 365 EU Data Boundary enough for sovereignty?
For most current EU government tenders, particularly when combined with customer-managed keys held in an EU region, yes. For the strictest interpretations under the forthcoming Cloud and AI Development Act, probably not on its own. Pairing it with sovereign tooling for the most sensitive contract data, ring one in this post, gives you a credible posture across the range of evaluations you are likely to encounter.